QR codes have revolutionized our digital interactions by allowing us to make a simple payment, see the menu in a restaurant, or download an app at a music festival with just a quick scan on our phone.
However, amidst their convenience lies a hidden security risk that many overlook. QR code phishing, or Quishing, is gaining popularity among fraudsters when stealing user accounts and payment information.
Easy for users, easy for fraudsters
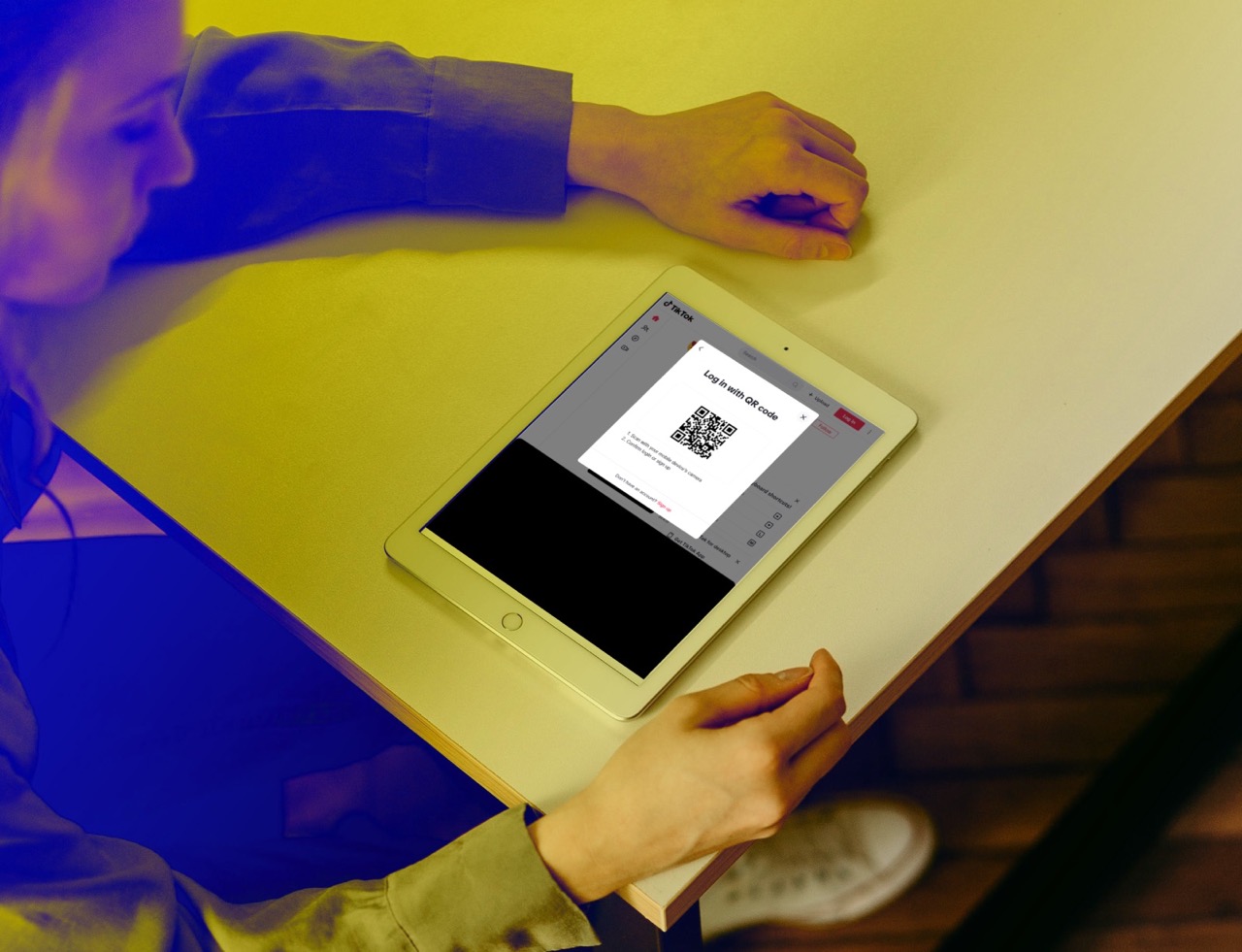
QR codes are often used by services to make the sign-in process and sharing of information easier and more user-friendly. A common example can be signing into your account from a new device, where instead of typing the username and password, you can simply scan the presented QR code from the app and seamlessly log in.
While this makes the process simple, it can be easily abused. The most common fraud targets are Google and Microsoft accounts, however, attackers are also trying to impersonate subscription and parcel delivery services.
How does it work?
Fraudsters send out well-crafted emails impersonating the service usually along the lines that there was “an issue with your payment” or “a suspicious login was detected”, prompting the user to solve the fictional issue by scanning the QR in order to log in and resolve it. Scanning the code, however, leads to a fraudulent website that will steal user’s credentials.
Quishing campaigns have been spotted targeting both end-users and enterprises worldwide. This technique is highly beneficial for the attackers for multiple reasons:
- While phishing links are scanned by most email security solutions, a simple image with a code will go undetected and the final link destination is obscured from the user until they scan it.
- QR codes also naturally redirect people to use their phones in order to scan them. Due to a smaller screen, users are usually less vigilant when it comes to checking the links.
Common Quishing strategies
The recent trend shows that almost 25% of phishing attacks now abuse QR codes. Usual attack themes can be:
- Fake notification of a security issue on your account, where attackers may claim that you have to log in using the QR code.
- Fraudulent surveys or quizzes may gather your personal information.
- Links to fake App stores that may download a malicious application into your device.
- Fraudulent two-factor authentication notifications. Upon scanning and confirming it unintentionally, the attacker gets access to your account.
Having Protective DNS, such as the one provided by Whalebone, can safeguard users against the links embedded in the QR code, as the security solution checks the link destination in the background even on people's phones, preventing access to the fraudulent site.



